American Lookout Headlines receives compensation from affiliate partners for links on the site. Here's our complete list of Affiliate sites.
First Column 1
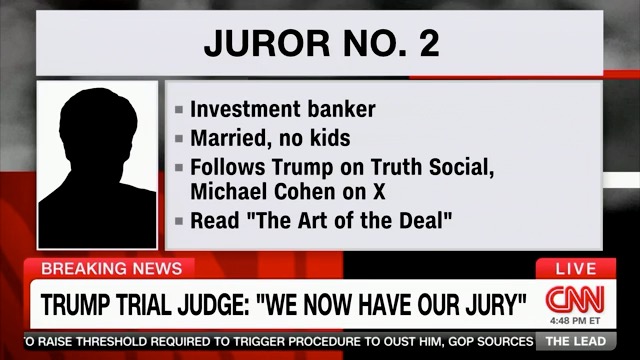
- Great News For Trump?
- New Panel Of Jurors Questioned For Trump Trial [Epoch]...
- Juror Dismissed In Trump Case Over Concerns Parts Of Her Identity Made Public...
- ...2 Jurors Dismissed In Trump Criminal Trial [Epoch]
- Barr Calls Bragg's Case Against Trump An "Abomination"...
- ...Says He Will Vote for Former President
- Trump And Polish President Meet At Trump Tower [Epoch]...
- Trump Lawyers Say Key Witness Refused Subpoena As Day 3 Of ‘Hush-Money’ Trial Starts [Epoch]...
NR Only Headline
Advertisement
First Column 2
If you like American Lookout Headlines, please bookmark us in your browser.
First Column 3
First Column 4
First Column 5
- US House Judiciary Committee Probes Biden Administration’s Collusion With Brazil’s Socialist Government Draconian Censorship...
- Law College 'Anti-Racism' Fellow Caught on Camera Piling Vicious Hatred on 'Ugly...Little Jewish People'...
- How Social Media Censorship May Impact the 2024 Presidential Election [Epoch]...
First Column 6
- Tucker: Why Do Reddest States Produce Dumbest Republicans?
- Purple-Haired Congresswoman Goes Berserk In Bizarre Rant...
- Shocking Report Reveals Disney's 'Star Wars' Box Office Has Failed to Cover the Cost of the Franchise...
- Students WALK OUT Of Nebo School District In Utah Protesting “Furries” That Bite and Hiss, Litter Boxes In Bathrooms...
- ...Disney’s Marvel Division Announces Layoffs, Output Reduction After Woke Flops
- Whistleblower: Gender Patients Begged To 'Have Body Parts Put Back On'...
"
Websites
- Gateway Pundit
- WLT Report
- The Epoch Times
- Conservative Brief
- Vigilant News
- 100 Percent Fed Up
- Trending Politics
- Big League Politics
- Freedom First Network
- New York Sun
- New York Post
- Right Side Broadcasting
- Conservative Treehouse
- People's Pundit Daily
- Zero Hedge
- Patriots.win
- Lucianne
- One America News Network
- Legal Insurrection
- Wayne Dupree
- Free Republic
- Intellectual Froglegs
- Western Journal
- Steve Bannon's War Room
Second Column 1
- FBI Director Issues Warning...
- ...Chinese Hackers Waiting To Attack US Infrastructure
- Hunter Biden Appealing Gun Charge Ruling Citing Defunct ‘Immunity’ Deal [Epoch]...
- Senate Dismisses Mayorkas Impeachment Articles...
- ...Johnson ‘Deeply Disappointed’ Senate Democrats Tossed Mayorkas Impeachment Charges [Epoch]
- National Guard Captain Testifies: Forced to Stand Down Until 5 pm on J6...
Second Column 2
Second Column 3
MyPillow (NR)
Get the American Lookout Headlines daily newsletter
Second Column 5
Second Column 6
- The UN Security Council Is About To Vote For A Palestinian State And Only A U.S. Veto Can Stop It...
- House Passes More Iran-Related Measures Following Its Attack on Israel [Epoch]...
- After Crazed Man Attacks Beloved Bishop, His Jaw-Dropping Response Inspires the Entire World...
- Individual Arrested In Connection With Attempted Zelensky Assassination...
- NATO Gets NEW Surprising Applicant...
Telegram Accounts
Contact Us
Send Tips
Third Column 1
Third Column 2
Third Column 3
Third Column 4
Third Column 5
Third Column 6
Third Column 7: Facebook Links
Websites
- Gateway Pundit
- WLT Report
- The Epoch Times
- Conservative Brief
- Vigilant News
- 100 Percent Fed Up
- Trending Politics
- Big League Politics
- Freedom First Network
- New York Sun
- New York Post
- Right Side Broadcasting
- Conservative Treehouse
- People's Pundit Daily
- Zero Hedge
- Patriots.win
- Lucianne
- One America News Network
- Legal Insurrection
- Wayne Dupree
- Free Republic
- Intellectual Froglegs
- Western Journal
- Steve Bannon's War Room